Quick Bit: A new variant of the RedLine Stealer malware has been discovered, utilizing Lua bytecode for stealth and effectiveness.
Full Story:
A new information stealer has been found leveraging Lua bytecode for added stealth and sophistication, findings from McAfee Labs reveal.
The cybersecurity firm has assessed it to be a variant of a known malware called RedLine Stealer owing to the fact that the command-and-control (C2) server IP address has been previously identified as associated with the malware.
RedLine Stealer, first documented in March 2020, is typically delivered via email and malvertising campaigns, either directly or via exploit kits and loader malware like dotRunpeX and HijackLoader.
The off-the-shelf malware is capable of harvesting information from cryptocurrency wallets, VPN software, and web browsers, such as saved credentials, autocomplete data, credit card information, and geolocations based on the victims’ IP addresses.
Over the years, RedLine Stealer has been co-opted by several threat actors into their attack chains, making it a prevalent strain spanning North America, South America, Europe, Asia, and Australia.
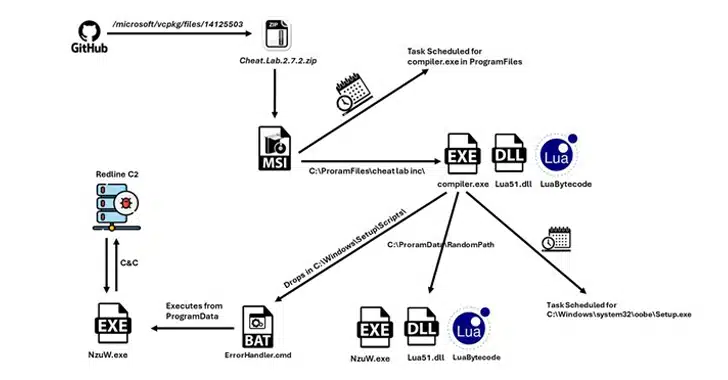
The infection sequence identified by McAfee abuses GitHub, using two of Microsoft’s official repositories for its implementation of the C++ Standard Library (STL) and vcpkg to host the malware-laden payload in the form of ZIP archives.
It’s currently not known how the files came to be uploaded to the repository, but the technique is a sign that threat actors are weaponizing the trust associated with trustworthy repositories to distribute malware. The ZIP files are no longer available for download from the Microsoft repositories.
The ZIP archive (“Cheat.Lab.2.7.2.zip” and “Cheater.Pro.1.6.0.zip”) masquerades as a game cheat, indicating that gamers are likely the target of the campaign. It comes fitted with an MSI installer that’s designed to run the malicious Lua bytecode.
“This approach provides the advantage of obfuscating malicious stings and avoiding the use of easily recognizable scripts like wscript, JScript, or PowerShell script, thereby enhancing stealth and evasion capabilities for the threat actor,” researchers Mohansundaram M. and Neil Tyagi said.
In an attempt to pass the malware to other systems, the MSI installer displays a message urging the victim to share the program with their friends in order to get the unlocked version of the software.
The “compiler.exe” executable within the installer, upon running the Lua bytecode embedded within the “readme.txt” file present in the ZIP archive, sets up persistence on the host using a scheduled task and drops a CMD file, which, in turn, runs “compiler.exe” under another name “NzUw.exe.”
In the final stage, “NzUw.exe” initiates communications with a command-and-control (C2) server over HTTP, the aforementioned IP address attributed to RedLine.
The malware functions more like a backdoor, carrying out tasks fetched from the C2 server (e.g., taking screenshots) and exfiltrating the results back to it.
The exact method by which the links to the ZIP archives are distributed is presently unknown. Earlier this month, Checkmarx revealed how threat actors are taking advantage of GitHub’s search functionality to trick unsuspecting users into downloading malware-laden repositories.
The development comes as Recorded Future detailed a “large-scale Russian-language cybercrime operation” that singles out the gaming community and leverages fake Web3 gaming lures to deliver malware capable of stealing sensitive information from macOS and Windows users, a technique called trap phishing.
“The campaign involves creating imitation Web3 gaming projects with slight name and branding modifications to appear legitimate, along with fake social media accounts to bolster their authenticity,” Insikt Group said.
“The main webpages of these projects offer downloads that, once installed, infect devices with various types of “infostealer” malware such as Atomic macOS Stealer (AMOS), Stealc, Rhadamanthys, or RisePro, depending on the operating system.”
It also follows a wave of malware campaigns targeting enterprise environments with loaders such as PikaBot and a new strain called NewBot Loader.
“Attackers demonstrated a diverse range of techniques and infection vectors in each campaign, aiming to deliver the PikaBot payload,” McAfee said.
This includes a phishing attack that takes advantage of email conversation hijacking and a Microsoft Outlook flaw called MonikerLink (CVE-2024-21413) to entice victims into downloading the malware from an SMB share.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
Partner content, here is the link to the original article Read More

![[VIDEO] Meghan McCain Just Can’t Stop Blasting Biden Lately…](https://manateeherald.com/wp-content/uploads/2021/06/300-4IokkF.jpeg)