How to use VPN to access blocked websites?
Governments and regimes across the globe use censorship as a tool to control the flow of information. This article highlights easy ways to bypass censorship, especially how one can use VPN to access b
 77°
77°
Governments and regimes across the globe use censorship as a tool to control the flow of information. This article highlights easy ways to bypass censorship, especially how one can use VPN to access b

With the help of malicious insiders, a fraudster was able to install malware and remotely divorce iPhones and other handsets from the carrier’s U.S. network — all the way from Pakistan.
Originally
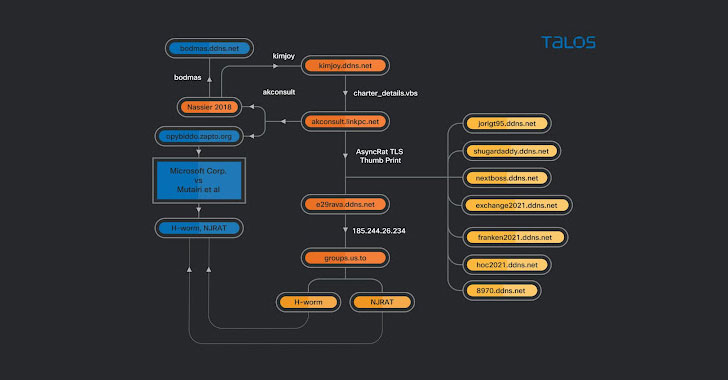
A targeted phishing campaign aimed at the aviation industry for two years may be spearheaded by a threat actor operating out of Nigeria, highlighting how attackers can carry out small-scale cyber offe

Here’s a look at the most interesting product releases from the past week, featuring releases from Alation, IDrive, Hornetsecurity, Palo Alto Networks, Qualys, ThreatConnect and Titania.
Qualys Pa

Over $133m has already been lost this year to romance scams, with victims increasingly urged to invest in fraudulent cryptocurrency opportunities, according to the FBI.
A new Public Service Announceme